Cybersecurity risks happen on week one
The First Week Mistake Nobody Plans For
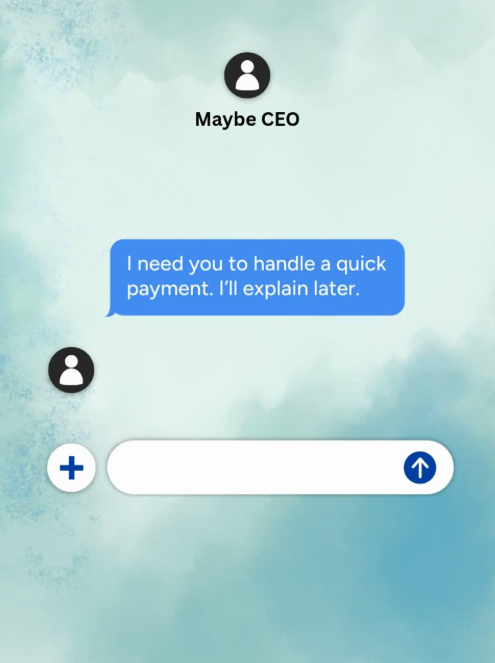
An email comes in from the “CEO” asking for a quick payment.
It feels urgent and looks legit.
The employee is only on day four.
They don’t want to be the employee who ignored the CEO, so they help.
That’s all it takes.
Why the first week is the most dangerous week
Every spring, businesses bring in a new wave of employees largely made up of recent graduates and summer interns stepping into their first roles. For companies, it’s onboarding season. For attackers, it’s something else entirely.
According to Keepnet Lab’s 2025 New Hires Phishing Susceptibility Report, CEO impersonation emails are 45% more likely to succeed with new hires than with experienced employees.
Attackers don’t go after your most seasoned people. They go after the ones who are still learning the ropes because there’s a window at the beginning where everything is unfamiliar and nothing feels certain.
A new employee doesn’t know what a typical request looks like. They don’t know how the CEO usually communicates. They haven’t had time to build instincts or confidence, and cybercriminals take advantage of that uncertainty.
But here’s the thing: The new employee isn’t the problem. The most dangerous employee isn’t careless. It’s the one trying to be helpful.
If you run a business, you probably already know exactly who on your team would respond first.
The real gap isn’t training. It’s the system.
Now think back to that employee’s first day.
Their laptop wasn’t ready. Access hadn’t been fully set up. Their email account was still being created. They borrowed someone else’s login to check something quickly. They saved a file locally because they couldn’t access the shared drive. They used their personal phone to look up a client number because it was faster.
None of that felt risky. It felt like being resourceful. Like doing what needed to get done on a hectic first day.
But in that first week, before everything is fully in place, a few important things happen quietly. Shared credentials create accounts nobody tracks, files end up outside of your backup systems, a personal device touches your business data, and no one explains what to do if something feels off.
The same Keepnet report found that new employees are 44% more susceptible to phishing than tenured staff. That gap doesn’t come from carelessness. It comes from chaos. When onboarding is chaotic, security becomes optional. That’s the environment the phishing email walks into.
The attack didn’t create the vulnerability. The first day did.
What a prepared first day looks like
Fixing this doesn’t require a long security presentation on day one. It requires three things to be ready before the person walks in the door.
- Their access is configured, not improvised. That means the laptop is ready, credentials are created and permissions are clearly defined. No borrowing logins, no temporary workarounds and no “we’ll sort that out later this week.”
- They know what a normal request looks like in your business. This can be a quick, 10-minute conversation. Does the CEO ever email about payments? Does anyone? What should they do if something feels off? This isn’t formal training; it’s basic orientation.
- They have somewhere to ask questions without feeling foolish. The employee who hesitated before clicking that email probably would have asked someone if they’d known who to ask. Most first-week mistakes happen quietly because new hires don’t want to look inexperienced.
Give them a person. Give them a process.
Most security mistakes don’t happen when someone ignores the rules. They happen when someone doesn’t know the rules yet.
Maybe your onboarding is already solid. Maybe your team is small enough that first days feel more personal rather than procedural. But if you’ve ever had a new hire improvise their way through week one — or if you’re planning to bring someone on this spring — it’s worth a conversation before that Tuesday email arrives.
Call us at 909-256-6202 or book a quick discovery call.
Author
Josue Nolasco
I'm a former US Marine infantryman who made a switch to IT to provide cyber security services to SMB's. I'm as much a child of technology as I am of the great outdoors. I like spending time playing, experimenting with, and learning new technologies and whenever possible taking camping trips with friends and family.

